Contact · Newsletter · DEUTSCH
Various EU regulations, most of which were launched in 2022, give cybersecurity a completely new significance for networked machines and plants as well, in other words, everything that is now grouped together under the generic term "Operation Technology" (OT).
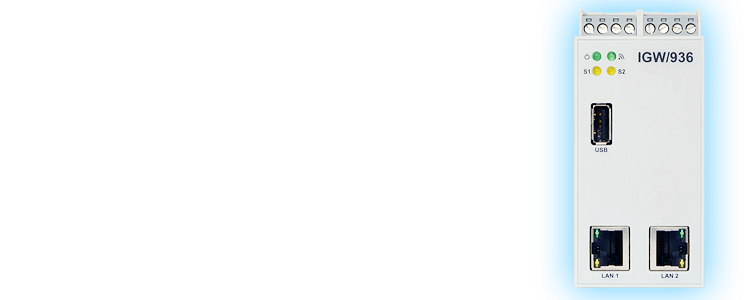
In the context of networked machines and plants, protection against cyber attacks is a demanding challenge, especially at the connection points between IT and OT networks. And this is exactly what the multifunctional OT/IT gateway IGW/936A was developed for.
The IGW/936A offers a wide range of configuration options that can be individually adapted to the specifics of an OT/IT integration.
Based on an innovative service-oriented gateway concept, the maximum possible cybersecurity can therefore be realized for a specific task.
Further applications for the IGW/936A are:
The adjacent figure shows the IGW/936A as an infrastructure module for domain isolation between the Ethernet-based networks of an IT and OT environment.
In addition, various OT modules in RS485-based bus systems, such as Modbus RTU, can be addressed from an Ethernet-based IT network via an IGW/936A.
Thereby an access rights management down to the single Modbus data point is possible.
A virtual patch does not close the security gap of a faulty application or firmware of a component. Instead, it uses an external intermediate or isolation layer to ensure that the vulnerability cannot be exploited by external access for cyber attacks. The following illustration describes a fictitious example with the IGW/936A.
There is a component within the OT network with a known vulnerability in the TCP/IP protocol stack. This vulnerability can be used to put the component into an inactive state, which can only be exited by interrupting the supply voltage.
A software update is not available for this component. However, as the component has special properties for the entire system operation, it cannot simply be replaced by another model.
The data flow of the connection process is analysed with regard to external access to the affected component.
It turns out that an IT application exists to manage the configuration and operating data for the component. HTTP(S) is used for this. In this respect, access from the IT network to the component in the OT network cannot be dispensed with.
A piece of software with an HTTP(S) proxy server function is developed for the connection process and installed on the IGW/936A via a patch management server. This prevents direct access from the IT network to the affected component; only indirect proxy access is now possible.
The data flow of the proxy server function on the IGW/936A creates two HTTP(S) connections:
The proxy server function forms an HTTP(S) server in the direction of the IT network and an HTTP(S) client in the direction of the faulty OT component.
| Single Board Computer | |
|---|---|
| Model | DIL/NetPC DNP/8331 |
| Processor | |
| Manufacturer / Type | Sochip S3 with ARM Cortex-A7 CPU |
| Clock speed | 1008 MHz |
| Memory | |
| RAM | 128 MB DDR3 SDRAM |
| Flash | 8 GB NAND Flash mass storage for operating system and application software |
| Interfaces | |
| Ethernet | 2x 10/100 Mbps (RJ45) |
| USB | 1x USB 2.0 Host |
| Serial I/Os | 1x RS485 serial port (screw terminal) 1x RS232/RS485 serial port (screw terminal) |
| Special Functions | |
| RTC | 1x Real Time Clock |
| Watchdog | 1x Timer Watchdog (hardware-based, software-configurable) 1x Power supervisor (hardware-based) |
| Displays / Control Elements | |
| LEDs | 1x Power 1x Status 1x System status (programmable) 1x VPN-Status (programmable) |
| Electrical Characteristics | |
| Power supply | 12 .. 24 VDC ) from external power suppl |
| Power consumption | < 10 W |
| Mechanical Characteristics | |
| Protection class | IP20 industrial case for 35 mm DIN-rail mounting |
| Mass | < 270 g |
| Dimensions | 112 mm x 100 mm x 45 mm |
| Operating temperature | 0 .. 60 °C |
| Standards and Certifications | |
| EMC | CE |
| Environmental standards | RoHS, WEEE |
| Software | |
|---|---|
| Operating System | SSV Debian Buster Linux |
| Boot Loader | U-Boot boot loader with A/B dual boot partitions |
| Administration | SSV/WebUI plus firmware |
| Security | TCP/IP protocol stack with IPv4 and IPv6 support and various security protocols |
| Firewall | netfilter + iptables, UDP/TCP-/application firewall |
SSV SOFTWARE SYSTEMS
Dünenweg 5
30419 Hannover
Phone: +49(0)511 · 40 000-0
Fax: +49(0)511 · 40 000-40
© 2026 SSV SOFTWARE SYSTEMS GmbH // All rights reserved.
ISO 9001:2015